Perhaps you have never wondered how much personal information your sim card stores and how attractive these little chips are to cybercriminals.
Sim cards contain much more information than your cell phone number, in addition to contacts you can save call records, photos, videos and even bank account passwords and passwords.
They are a holy grail for hackers as by gaining access to your Sim, they will be able to carry out multiple cybercrimes that can compromise your money or identity.
Index
- What is Sim Swapping or Sim Kidnapping?
- How to protect yourself?
- What is an encrypted Sim?
- Meet the Encrypted Sim
What is SIM-Swapping or SIM hijacking?
This technique, which has been experiencing staggered growth, has several phases to carry out its mission. Initially, cybercriminals seek to confuse, manipulate, or even buy off vendors who work for cell phone companies in order to transfer customer numbers to networks controlled by them. Once they do this, hackers can create fake Wi-Fi networks, scam pages like your bank’s that look just like the real thing but aren’t, fake URLs that they send to the email, or even totally fake mobile apps that try to lead the victim to hand over their personal passwords.
Once the victim falls into the trap and enters one of these fraudulent options, the hacker will be able to receive the verification codes that they send to the cell phone by SMS text message and thus be able to access any type of personal information of the hacked person.
Worst of all, the crime does not end here. Once the criminal has access to your information he proceeds to commit another crime, impersonation. Having the data of the victim and having access to all her privacy, the offender can visit the offices of mobile phone operators pretending to be you and look for a duplicate or copy of the Sim card. On his part, the victim will not notice anything until his sim card begins to have repeated or permanent signal failures, his calls have interference, or the mobile device begins to overheat for no reason.
Once the hacker accesses this data, he can easily enter and transfer money from your bank account, request credits in your name, download paid applications, use credit cards or access any site pretending to be the victim. Usually, most of the pages use two-step authentication by sending an SMS to the mobile number, which will be controlled by the hacker.
In 2019, one of the most notorious victims of this crime was Twitter CEO Jack Dorsey, who suffered identity theft through a Sim kidnapping in which they had access to his Twitter account and published racist and offensive content. The impact was such that Twitter announced that it would withdraw the sending of messages to the platform through text messages.

How to protect yourself?
Unfortunately, due to the few laws in the state and the few controls by mobile phone service providers, it is very difficult to control this crime and it has become one of the favorites of cybercriminals who are claiming more and more victims. If we wait for the companies that provide us with data and calling plans to do something, we will be wasting time, unfortunately, it is up to us to protect and ensure the privacy and security of our information.
Some of the things you can do to deal with SIM-Swapping is to replace SMS authentication with an application that fulfills this function. Today there are different apps from companies like Google or Microsoft that can help with this issue, however they are not enough since they are also manipulable. So if what you are looking for is total and permanent security, it is advisable to choose to change your common Sim for an encrypted Sim or an encrypted Sim .

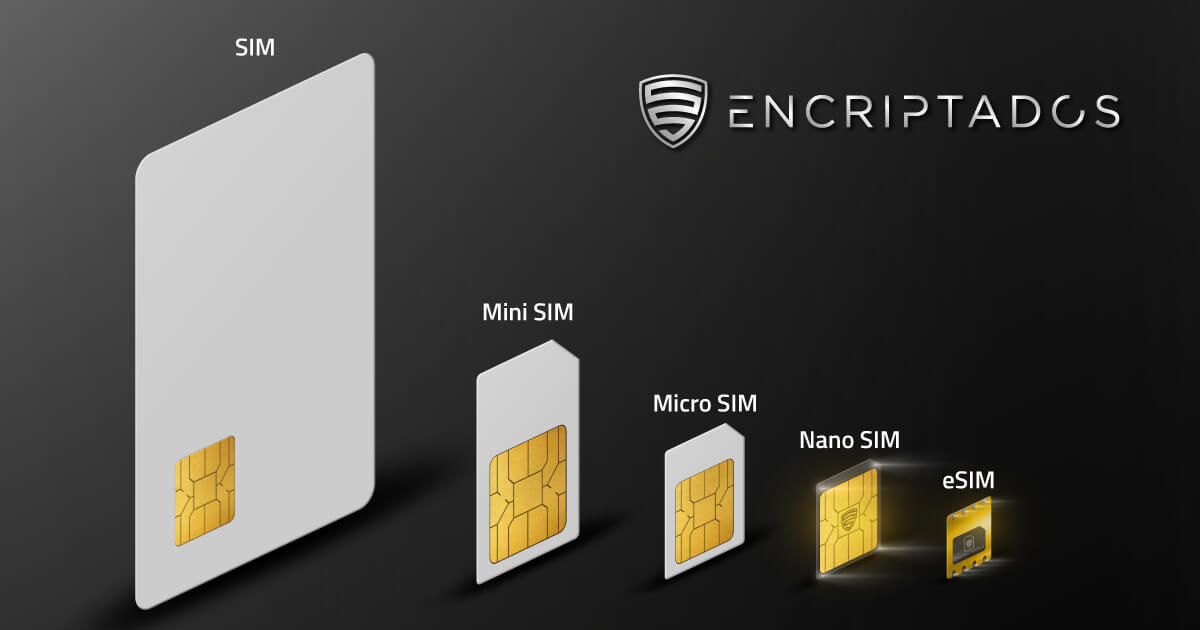
What is an Encrypted Sim?
Encrypted Sims are the opposite of a common Sim since instead of putting your personal data and information at risk, what they seek is to protect you from this crime and many others in which we are at risk every day.
Encrypted Sims use state-of-the-art military technology that guarantees that all the information you transmit from your phone and enter your phone will be encrypted and with a higher security layer that will not allow hackers to access your privacy. These cards do not issue an IMSI which makes it impossible to trace the origin of the connection. on the contrary, the IMEI, which is the identification number that your cell phone has and with which they can identify you, will be hidden, so that it is impossible to associate the SIM to a phone.
It may interest you: Why have an encrypted sim?
On the other hand, encrypted SIM card providers will offer you greater anonymity when purchasing it, you will not have contracts so your personal data will not be at risk of being manipulated by third parties and even if a cybercriminal impersonates you and search for your information will not find anything, because not even the encrypted Sim service provider has access to your information.
Get to know the Encrypted SIM
The Encrypted SIM connects you anywhere and offers you the security and privacy you are looking for. It is a solution to one of the largest and most common security breaches in the world. Our goal is to provide you with total protection by having an additional layer of security, complete anonymity, no contract and no time limit on the consumption of your plan.
Having the Encrypted SIM means having a private network provider that will be in charge of providing you with security and guaranteeing you total anonymity, preventing your information from being manipulated, shared or sold.
It is the ideal option to protect yourself and take your privacy to another level, if you combine it with encrypted cell phones and encrypted applications you ensure that all your information and communications will be 100% secure.